Scans
Challenge:
ESU's IT staff noticed some peculiar traffic from DEADFACE at the beginning of the attack. They sent a series of handshakes - the IT staff is stumped as to what DEADFACE was trying to do.
What type of scan did DEADFACE launch first?
Submit the flag as
flag{scantype}.
Solution:
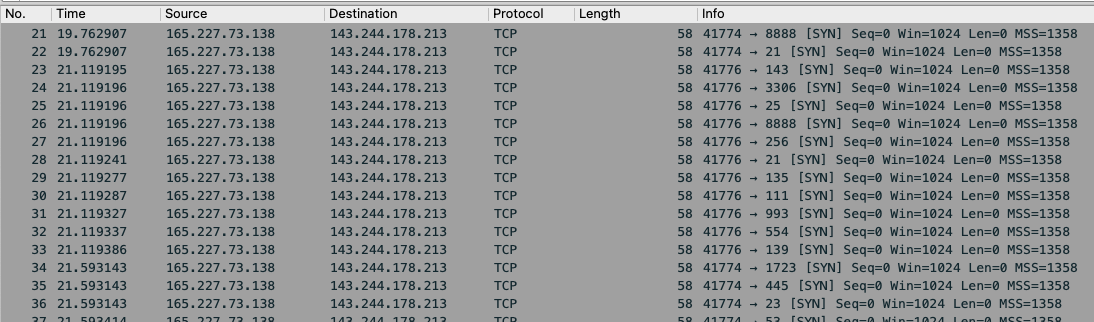
Upon opening the provided PCAP in Wireshark the overwhelming number of SYN packets, in a very short amount of time, is hard to miss:
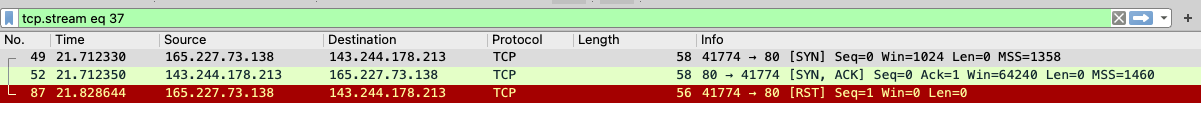
Additionally, we know from the earlier Toolbox challenge that Nmap was used to scan the server. Nmap's default scan mode is TCP SYN a.k.a "Stealth Scan", which sends a SYN packet to all the ports to be scanned, as if looking to establish 3-way handshakes (SYN, ACK, SYN-ACK), but sends a RST packet if/when the target replies with an ACK. This specific behavior can be seen in stream 37; here the target server replied with an ACK for port 80 and Nmap responded with a RST instead of a SYN-ACK:
The accepted flag was: flag{SYN}

Leave a comment