RansomWAR 2 - Indicators of YOU'RE HOSED!
Challenge:
An "Indicator or Compromise" (IoC) is a unique feature of a particular piece of malware. IoCs are often used to help virus scanners and network tools identify the malware so that it can be blocked.
The Dark Angel cryptoware has three network-based IoCs. Two of them are URLs that the malware connects to. The other is the HTTP UserAgent string. Enter one of the three as the flag for this challenge.
For the UserAgent string, don't enter the full header; only enter the UserAgent string itself, as in:
flag{python-requests/2.26.0}
… or …
For the URL, include the protocol, the server, and the full path, without the URL parameters, as in:
flag{http://darkangel.linode.com/mymalware/you-are-hosed.php}Only one of the three flags is required to complete the challenge.
Solution:
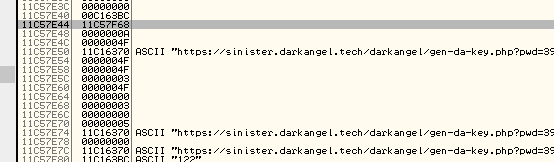
During the CTF we solved this challenge with a debugger on a VM without a network connection to quickly grab the first URL request attempt:
Following the competition we were curious about collecting all three IOCs, so we setup FakeNET-NG on an Ubuntu VM and configured it as a DNS/Gateway on our Windows10 VM.
10/16/22 02:38:32 PM [ DNS Server] Received A request for domain 'sinister.darkangel.tech'.
10/16/22 02:38:32 PM [ HTTPListener443] GET /darkangel/gen-da-key.php?pwd=bc331dab&shift=33 HTTP/1.1
10/16/22 02:38:32 PM [ HTTPListener443] Host: sinister.darkangel.tech
10/16/22 02:38:32 PM [ HTTPListener443] User-Agent: DARKANGEL_DEADFACE_CRYPTOWARE/0.3
10/16/22 02:38:32 PM [ HTTPListener443] Accept-Encoding: gzip
10/16/22 02:38:33 PM [ DNS Server] Received A request for domain 'sinister.darkangel.tech'.
10/16/22 02:38:33 PM [ HTTPListener443] GET /darkangel/gen-da-file.php?pwd=bc331dab&shift=33 HTTP/1.1
10/16/22 02:38:33 PM [ HTTPListener443] Host: sinister.darkangel.tech
10/16/22 02:38:33 PM [ HTTPListener443] User-Agent: DARKANGEL_DEADFACE_CRYPTOWARE/0.3
10/16/22 02:38:33 PM [ HTTPListener443] Accept-Encoding: gzip
The accepted flags were:
flag{DARKANGEL_DEADFACE_CRYPTOWARE/0.3}flag{https://sinister.darkangel.tech/darkangel/gen-da-key.php}flag{https://sinister.darkangel.tech/darkangel/gen-da-file.php}

Leave a comment