Database Crack
Challenge:
We did it! We managed to get a copy of a password database from
deephax. Can you crack the password to get into the database and see what things lie within?Submit the flag as
flag{flag text}.
Solution:
We identified the file provided in the challenge as a Keepass password manager database:
$ file mySecret.kdbx
mySecret.kdbx: Keepass password database 2.x KDBX
John the Ripper has a keepass2john utility for extracting the password hash from a Keepass database, which we leveraged to write the hash to a file for cracking:
$ ~/Tools/jtr/keepass2john mySecret.kdbx | cut -d: -f2 | tee database_crack.hash
$keepass$*2*60000*0*b8bb35396aa2cc7b81c8d1e68ef3baf23d20f781406946c280230d100173e739*63e6afc61de486d9855f0696918acfb2b6f59593d98f1fb23c6b41bb045ec0b4*e8c1e5981c84aa4f52be41271efaba41*3c567f9f005c33c0342e943ed1e37d343fa7215b103a6bfd9278ac4c265de41e*5f4030232f25e16e767fb31fbf7b69458f274f651659719dfa99fa1fe66715f5
Surprisingly, in our first cracking attempt we found that the password wasn't in the RockYou file:
$ hashcat -m 13400 -a 0 -w 4 database_crack.hash /data/wrdlists/rockyou.txt
...
Status...........: Exhausted
We could have run a new cracking session using the WeakPass2 list but Hashcat was estimating it would take ~20 hours on our cracking rig, which didn't seem appropriate for this CTF. Luckily, while browsing the various GhostTown threads to document clues, we spotted a wordlist posted by mirveal in the thread titled "More Bitcoin$$$$$".
Hashcat made short work of wordlist and produced the password in under 6 seconds:
Status...........: Cracked
complexpassword
We could then use the cracked password to unlock the Keepass database and retrieve the flag:
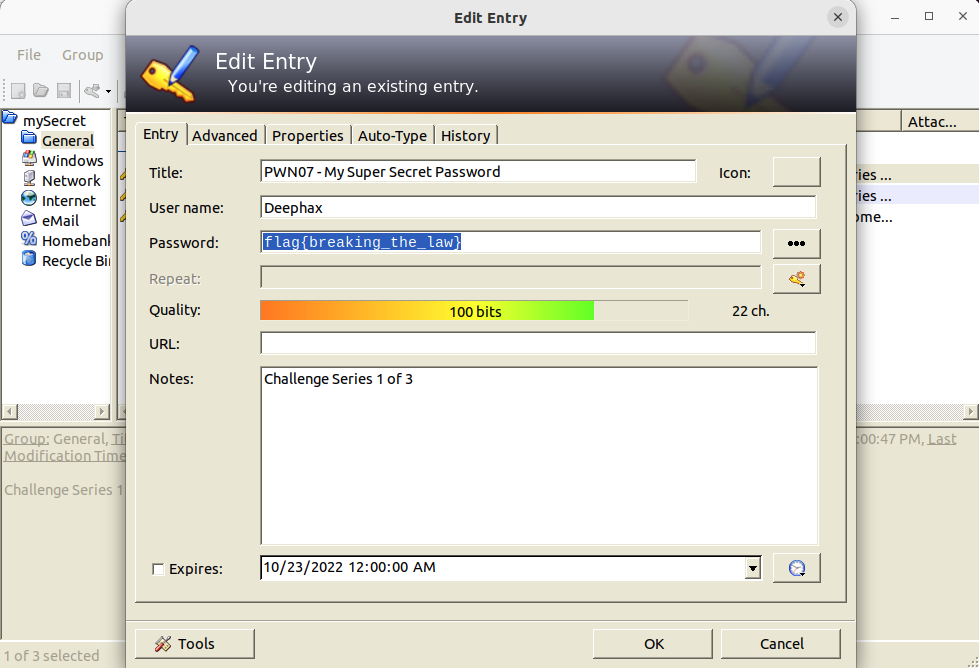 ```
```
The accepted flag was: flag{breaking_the_law}

Leave a comment