Mobility
Challenge:
Always wanted to calculate HMACs on your phone? Check out our new app! It supports 6 different algorithms.
Solution 1:
The provided challenge file was an Android Package Kit (APK), which can be unpackaged using unzip. I start every forensics challenge with a quick strings | grep (work smarter?) and was handed a quick win.
$ grep -rF 'flag{' *
Binary file classes.dex matches
$ strings classes.dex | grep -rF 'flag{'
(standard input):flag{classic_apk_decompile_shenanigans}
Given the flag contains classic_apk_decompile_shenanigans I have to assume this was not the challenge creator's intended solution.
Solution 2:
In the spirit of the challenge, here is the approach I would have taken had my first solution failed.
After unzipping the APK I converted classes.dex to a JAR file using dex2jar.
$ d2j-dex2jar.sh classes.dex
dex2jar classes.dex -> ./classes-dex2jar.jar
I then decompiled the JAR using JD-GUI and inspected the code in the com.congon4tor.mobility package. The first thing that caught my eye was the secret variable.
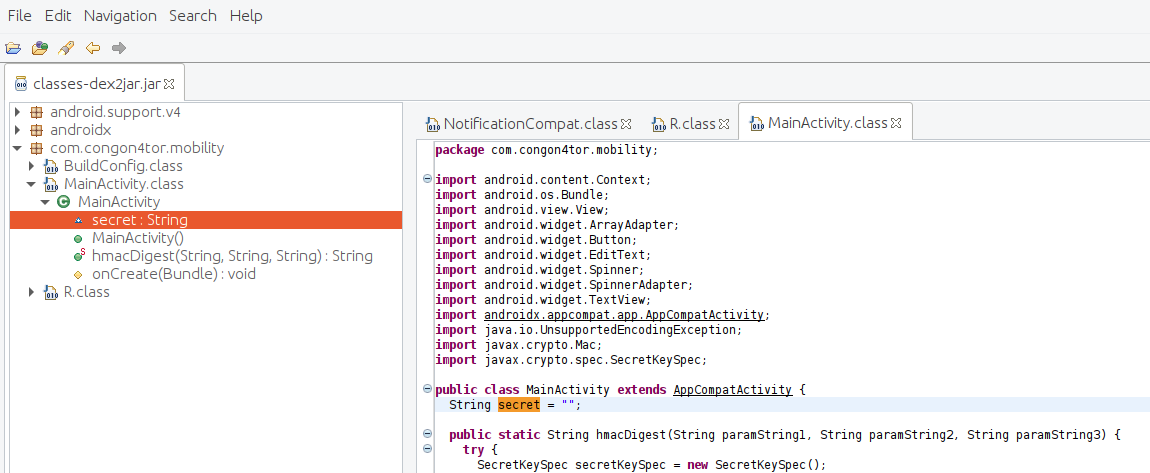
Scrolling though the code I saw that within the onCreate() function a value is assigned to the secret variable: this.secret = stringBuilder.toString(). The stringBuilder object is created in the same function with a for() loop appending individual decimal values to the string.
StringBuilder stringBuilder = new StringBuilder("");
for (byte b = 0; b < 39; b++) {
(new byte[39])[0] = 102;
(new byte[39])[1] = 108;
(new byte[39])[2] = 97;
(new byte[39])[3] = 103;
(new byte[39])[4] = 123;
(new byte[39])[5] = 99;
(new byte[39])[6] = 108;
(new byte[39])[7] = 97;
(new byte[39])[8] = 115;
(new byte[39])[9] = 115;
(new byte[39])[10] = 105;
(new byte[39])[11] = 99;
(new byte[39])[12] = 95;
(new byte[39])[13] = 97;
(new byte[39])[14] = 112;
(new byte[39])[15] = 107;
(new byte[39])[16] = 95;
(new byte[39])[17] = 100;
(new byte[39])[18] = 101;
(new byte[39])[19] = 99;
(new byte[39])[20] = 111;
(new byte[39])[21] = 109;
(new byte[39])[22] = 112;
(new byte[39])[23] = 105;
(new byte[39])[24] = 108;
(new byte[39])[25] = 101;
(new byte[39])[26] = 95;
(new byte[39])[27] = 115;
(new byte[39])[28] = 104;
(new byte[39])[29] = 101;
(new byte[39])[30] = 110;
(new byte[39])[31] = 97;
(new byte[39])[32] = 110;
(new byte[39])[33] = 105;
(new byte[39])[34] = 103;
(new byte[39])[35] = 97;
(new byte[39])[36] = 110;
(new byte[39])[37] = 115;
(new byte[39])[38] = 125;
stringBuilder.append((char)(new byte[39])[b]);
}
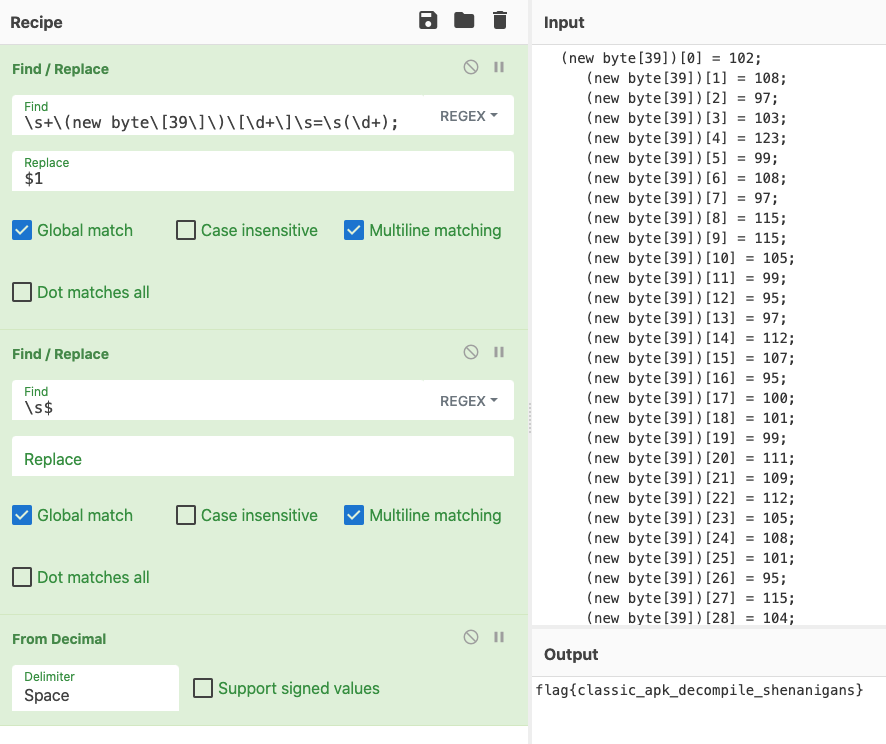
I pasted the sequence of code into CyberChef and wrote a recipe to extract the values and convert to ASCII.

Leave a comment